1. Intro
On January 8, 2023, thousands of demonstrators sympathetic to former President Jair Bolsonaro, falsely convinced that the presidential election had been stolen, stormed the nation’s Congress, Supreme Court and presidential offices in Brazil’s capital (Brasília – DF).
This article from The New York Times shows the exact moment when protesters broke through the police barrier and started the riots that culminated in the invasion and depredation of Brazil’s Congress, Supreme Court and presidential offices.
2. The UOL Report
On January 11, 2023, journalists Amanda Rossi and Lúcia Valentim Rodrigues published an article stating that “preparation for the coup act had an online map”.
According to the article, the online map pointed out 21 people responsible for the caravans that were supposed to transport demonstrators to the January 8 riots in Brasília.
3. My Maps
The map mentioned by the article was titled “Viagem para Praia” ("Beach trip") and was made using My Maps, a feature of Google Maps that allows you to create custom maps with shapes, lines, points, notes, photos and videos.
Maps made with "My Maps" have the following sharing options:
- Private;
- Share your URL with specific people;
- Make your map public: allow anyone to find your map.
That being said, My Maps URLs (Uniform Resource Locators) have a pattern: they begin with the string “https://www.google.com/maps/d/u/0/” and have a My Maps ID which is located after the string “mid=” and before the string “&ll=”.
Take, for instance, the My Maps for the “Walking Tour of Downtown Port Hope”
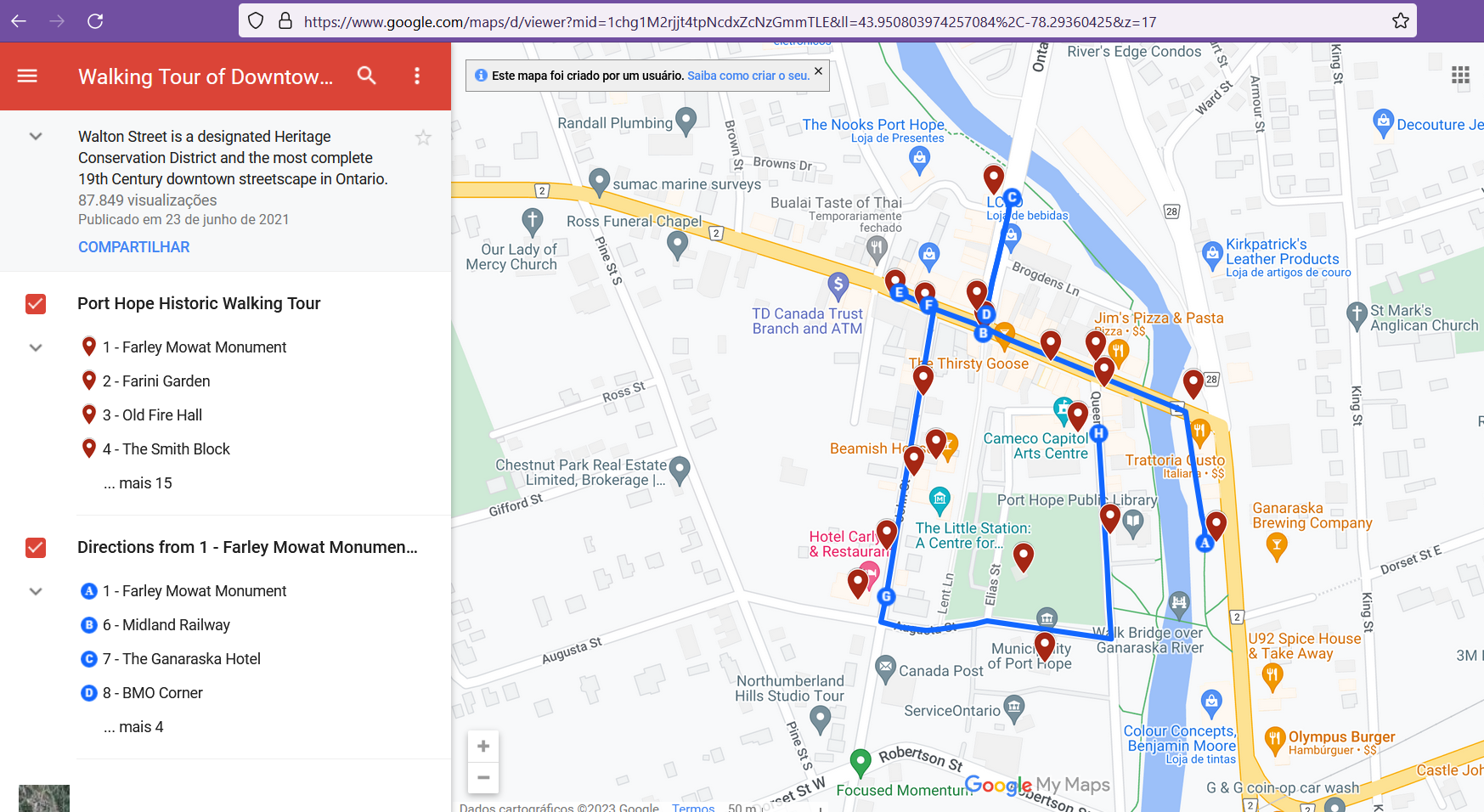
Figure 1 - My Maps for the “Walking Tour of Downtown Port Hope”.
In the above URL the My Maps ID is 1chg1M2rjjt4tpNcdxZcNzGmmTLE.
4. My Maps “Viagem para Praia”
Google My Maps instance called “Viagem para Praia” ("Beach Trip") found by reporters Rossi and Rodrigues was shared in a Telegram group once called “Caça e Pesca” and therefore the URL could be obtained by any member of that Telegram group.
The URL in question is as follows (several X’s were used to redact the My Maps´ ID since we don’t want to doxx people here):
https://www.google.com/maps/d/u/0/viewer?mid=1pr7p8Bzwtwd9ToPvXXXXXXXXXXXXXXX
My Maps “Viagem para Praia” (nowadays removed by the creator) had four layers representing four out of five brazilian regions:
- Região Sudeste (southwest region)
- Região Sul (south region)
- Região Centro-Oeste (center-west region)
- Região Nordeste (northeast region)
Each layer had several pins inserted in specific Brazilian cities as can be seen in the figure bellow.
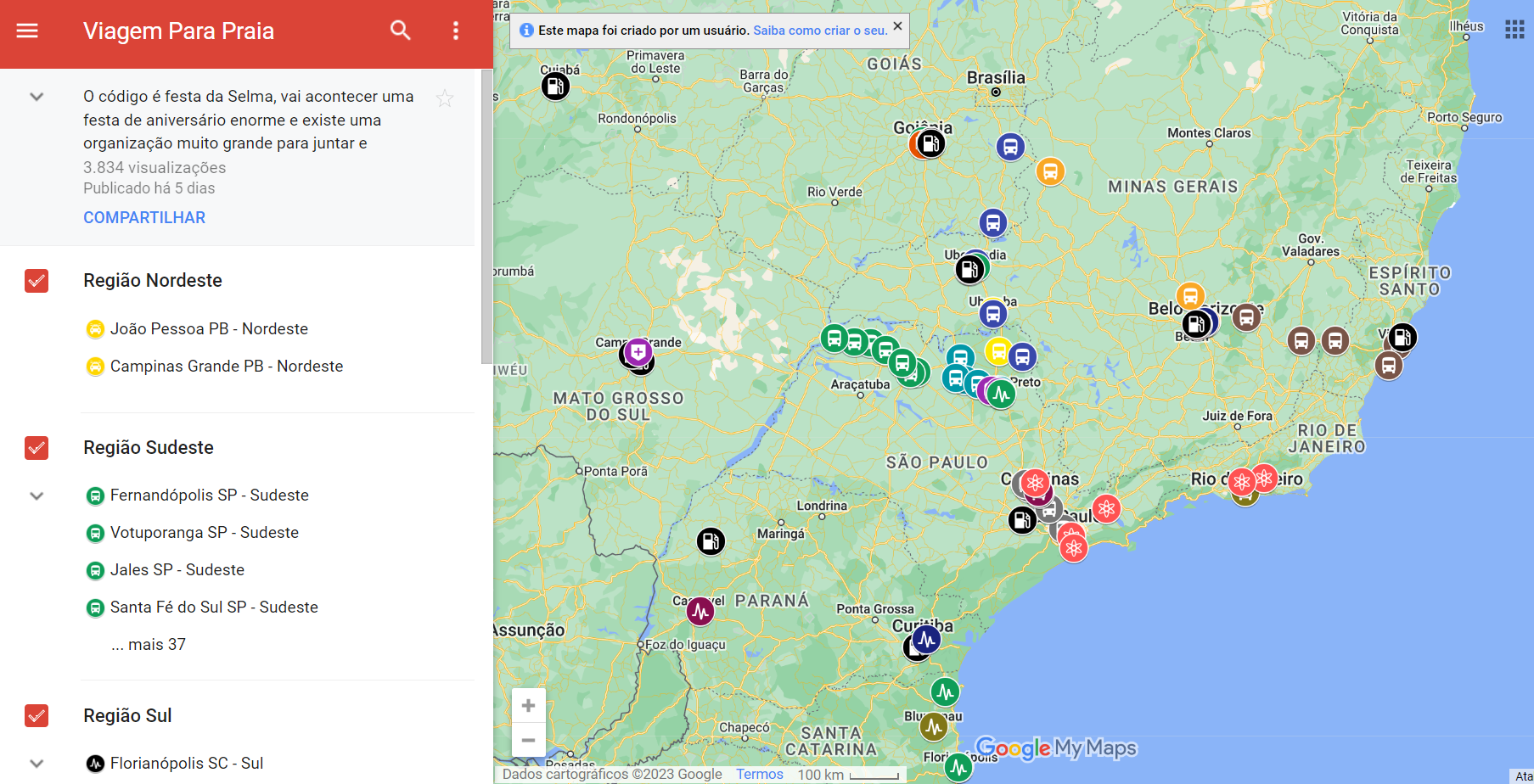
Figure 2 – Screenshot of My Maps “Viagem para Praia”
Clicking at a specific pin (or city for that matter) leaded users to find either Whatsapp accounts or a specific Telegram group associated to a person or group of people responsible from transporting demonstrators from that city (or region) to Brazil's capital (Brasília – DF).
Below is a screenshot showing an Whatsapp account associated with the city of João Pessoa – PB in the Northeast Region of Brazil.
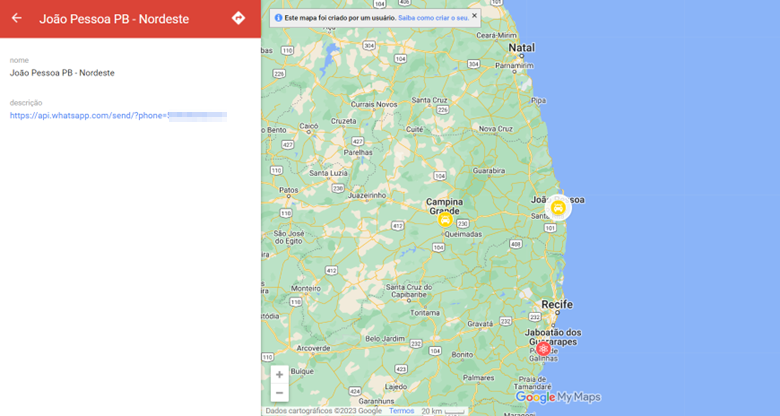
Figure 3 – Screenshot of My Maps “Viagem para Praia”
It´s important to highlight that January 8 riots were codenamed "Festa da Selma" ("Selm´s party) by the creator of the My Maps "Viagem para praia"
Some OSINT tactics, techniques and procedures (TTP) apply to this case. They're detailed below.
Given it's lenght, this write-up will be divided in two parts, dedicated to detail OSINT TTPs used to: (1) find who created “Viagem para praia” My Maps; (2) unveil the people responsible from transporting demonstrators from the cities listed in the map to Brazil's capital for January 8 riots.
5. Google Drive URL manipulation
The first idea to tackle “Viagem para praia” My Maps came from GONZO.
GONZO stated the manipulation of the URL Google uses for Google Drive abuse reporting could reveal the name used by the creator of “Viagem para praia” My Maps.
One can report abusive content in Google Drive’s files going to drive.google.com, right-clicking the file to be reported and then clicking “Report abuse”.
Doing that leads to a new browser tab with the following URL structure:
https://drive.google.com/abuse?id=XXX&authuser=0
Where XXX is the ID of the file to be reported.
That being said, what GONZO brilliantly suggested was to insert the "My Maps" ID in the place of the ID of the file to be reported, to see what would happen.. and it worked!
Proceeding like that lead us to a Google Drive abuse reporting page that yielded a name associated to “Viagem para praia” My Maps: ADIXXX CHAXX (X’s are used here to mask the actual words since we don’t want to doxx people).
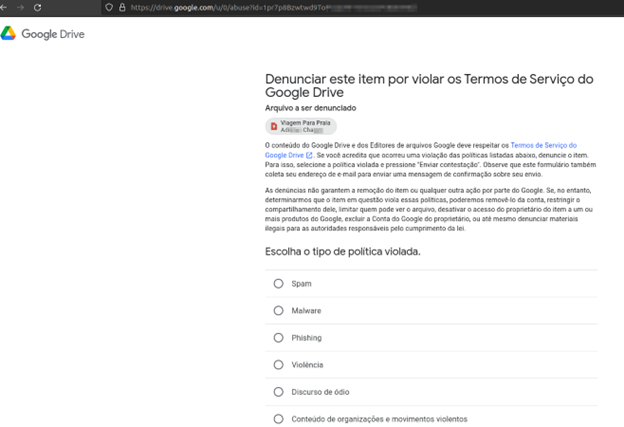
Figure 4 - Manipulation of Google Drive abuse URL
By the way, make sure that you follow GONZO at Twitter. He is a world class OSINT investigator.
6. GHUNT
GONZO also suggested that mxrch could come up with a solution to pull data from the investigated My Maps since he is THE reference when it comes to OSINT related to Google services.
Sidenote: mxrch is the creator of Ghunt, an offensive Google framework that can pull data from Gmail accounts, Google Drive accounts and GAIA IDs (GAIA ID stands for Google Accounts and ID Administration ID. If you want to know more, check out these two sector035 awesome articles about it: Grasp on Google IDs and Grip on Google IDs.
Ghunt's documentation doesn't mention that the script is able to pull data from "My Maps" URLs, but mxrch stated that Ghunt's Drive module is able to work out with My Maps links. And it works indeed!
Targeting “Viagem para praia” with Ghunt’s Drive module leads to several that points that are listed below.
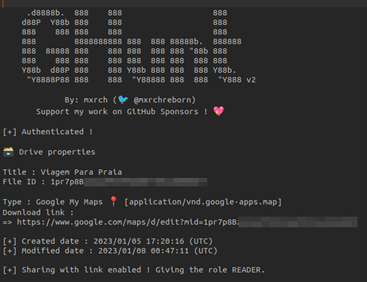
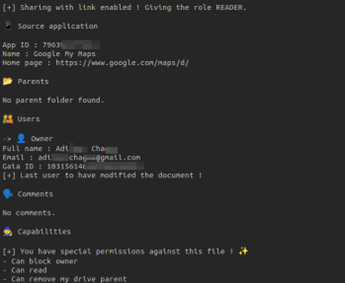
Figures 5 and 6 - Data pulled in 1/12/2023 from My Maps "Viagem para praia"
At this point it's clear that a person using Google account adiXXXchaXXX[@]gmail.com is the creator of My Maps “Viagem para Praia”.
But who is he? How could we put a face to a Gmail account?
Again, Ghunt is the solution to go. Ghunt's Gmail module leads to several data points when it targets the account adiXXXchaXXX[@]gmail.com.
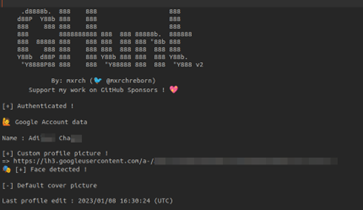

Figure 7 and 8 - Data points associated with adiXXXchaXXX[@]gmail.com
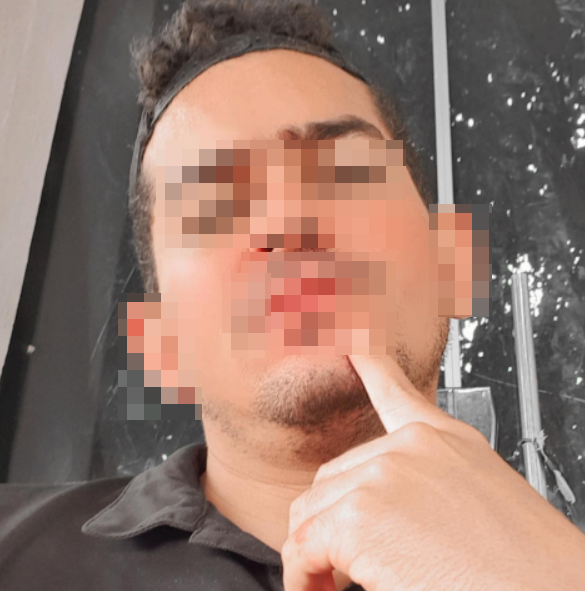
Figure 9 - adiXXXchaXXX[@]gmail.com profile picture
Make sure that you follow mxrch at Twitter, he is also a world class OSINT investigator. Also check his website.
7. Username Enumeration
Ok. Looks like we have an attribution at this point. Now is time to pivot to username adiXXXchaXXX and see what else can be found to corroborate everything that was pulled with Ghunt.
Snoop and Maigret led to several social media accounts with the username adiXXXchaXXX. All accounts had profile pictures very similar one to another and also similar to the Gmail account profile picture





Figures 10 to 14 - Social Network Profiles
It is worth mentioning that the Telegram account @adiXXXchaXXX was a member of the group (“Sudeste”) in which the My Maps “Viagem para Praia” was first published

Figure 15 - Telegram account @adiXXXchaXXX
Snoop also pointed out a Steam account where the city of Fernandópolis – SP is mentioned. This city (which is also mentioned in the Facebook account) is where most of adiXXXchaXXX[@]gmail.com Google reviews are located



Figures 16 to 18 - Steam Account and Google Reviews
Last but not least, we can also find a Twitter account and a TikTok account with the same username (both found with a traditional Google search) that show several pro-Bolsonaro posts.


Figures 19 and 20 - TikTok and Twitter
8. Final Thoughts - Part I Conclusion
At this point two conclusions can be drawn:
- (1) OSINT is a very, very powerful tradecraft;
- (2) Isaac Newton's quote “If I have seen further, it is by standing on the shoulders of giants.” is fully applicable to OSINT investigations.
Next time, in Part 2: The unveilment of people responsible from transporting demonstrators from the cities listed in “Viagem para a Praia” to Brazil's capital for January 8 riots.
To be continued...
